Sponsored by IBM
Sponsored by Neustar
2015 DDoS Impact & Response Study
Sponsored by IBM
Strengthening Networks and Endpoints with Behavior-Based Protection
Sponsored by Imperva
Web Application Firewalls Are Worth the Investment for Enterprises
Sponsored by IBM
Security Essentials for CIOs: Securing the Extended Enterprise
Sponsored by IBM
Security Essentials for CIO's: Establishing a Department of Yes
Sponsored by ISACA
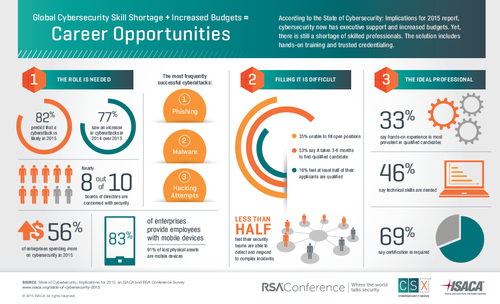
State of Cybersecurity: Implications for 2015 Infographic
Sponsored by Hitachi ID
Best Practices for Securing Privileged Access
Sponsored by IBM
Gartner Best Practices for Securing Hadoop
Sponsored by IBM
Data protection for big data environments
Sponsored by IBM