Cybercrime , Data Loss Prevention (DLP) , Fraud Management & Cybercrime
Australian Shipbuilder Hacked, Refuses to Pay Ransom
Austal Says Material Is Neither Sensitive Nor Classified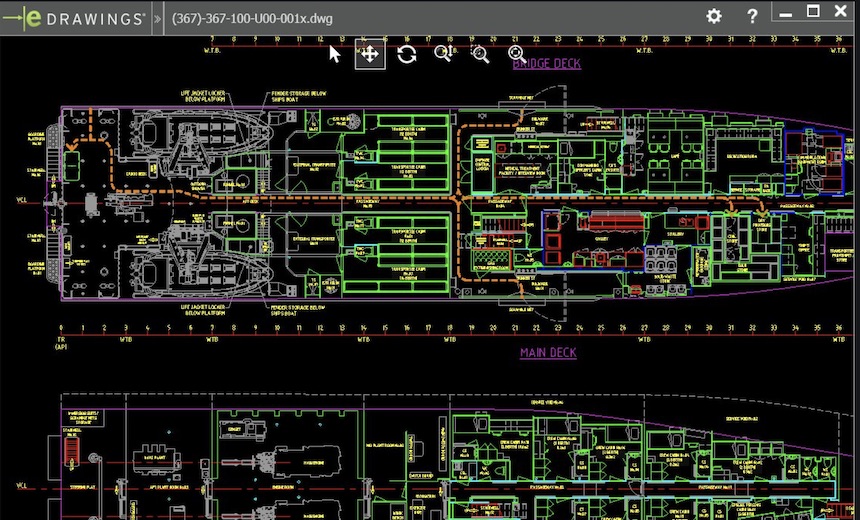
Australia's largest defense exporter says it hasn't responded to an extortion attempt after ship design schematics were stolen by a hacker.
See Also: The Alarming Data Security Vulnerabilities Within Many Enterprises
Austal, which is based in Henderson, Western Australia, is one of the country's largest shipbuilders; it has built vessels for the U.S. Navy.
The company, which is listed on Australia's ASX stock exchange, announced the breach late Thursday. The announcement came just a day after a security researcher in France posted screenshots on Twitter of the purported stolen data.
Austal says the material is neither sensitive nor classified and that it has taken steps to secure its data systems.
"The data breach has had no impact on Austal's ongoing operations," the company says. "Austal's business in the United States is unaffected by this issue, as the computer systems are not linked."
A spokesman for Austal contacted on Friday says he couldn't offer further information on the incident.
The breach exposed ship design drawings that are distributed to customers, fabrication subcontractors and suppliers, Austal says. It also exposed "some staff email addresses and mobile phone numbers." Those individuals have been informed as well as a "small number" of other stakeholders directly impacted by the breach, the company reports.
Austal has contacted the Australian Cyber Security Center and the Australian Federal Police. The Office of the Australian Information Commissioner, which enforces the country's data protection regulations "will be involved as required," Austal says.
The.Joker
A hacker going by the nickname "the.joker" advertised the material for sale on an underground forum earlier this week. Xylitol, a well-known French security researcher, posted screenshots of the the.joker's postings on Oct. 31, a day before Austal's announcement.
someone is selling @austal cad files on black a hat boardpic.twitter.com/ToVC9w7S4m
— Xylitol (@Xylit0l) October 31, 2018
Xylitol also wrote that he asked for samples of the data and received four, with timestamps that ranged from 2006 to 2017.
i contacted him, he sent me 4 random samples, timestamp from 2017 to 2006 pic.twitter.com/euIeNn153v
— Xylitol (@Xylit0l) October 31, 2018
The.joker claims to have dumped data from Austal's network PCs about a month prior. The zip file, which consisted of drawings and designs, is 75GB in size, the.joker claims.
Some of the sample images the.joker included in a forum posting were still live on Friday and indicated the material was posted there five days prior.
The material was being offered for 1 bitcoin, or about $6,300. That figure is likely far lower than whatever figure was presented to the company as a ransom.
Don't Pay Ransoms
Companies are increasingly being subjected to ransoms by hackers after their networks have been breached. Ransoms put companies in tough positions: risk public exposure of potentially embarrassing data, or risk paying a ransom and still face a chance the data could be released anyway.
Security experts and law enforcement generally advise against paying ransoms, even after incidents of file-encrypting malware. But some companies have viewed the situation as either a cost of doing business or a shorter route to recovery.
Late last month in the U.S, the city of West Haven, Connecticut, paid $2,000 to unlock 23 servers that had been infected with ransomware (see: Connecticut City Pays Ransom After Crypto-Locking Attack).
The city's attorney, Lee Tiernan, was quoted by the Associated Press as saying "research showed it was the best course of action."
If the city didn't have a backup file, it may have had little choice. But a compelling counter argument is that paying offers further incentive for criminals to continue with the schemes.